publications
publications by categories in reversed chronological order. generated by jekyll-scholar.
2026
- How (not) to Switch FHE Schemes: Framework and Attacks in the IND-CPA-D ModelGiacomo Santato and Riccardo Zanotto2026
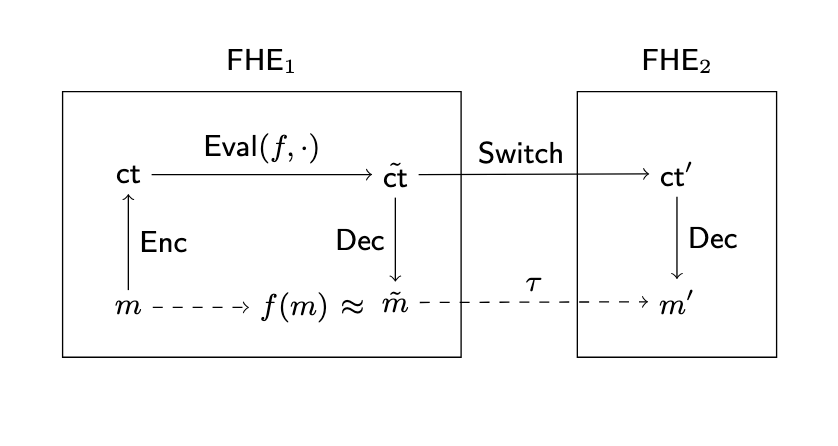
In this paper, we study the IND-CPA-D security of FHE schemes when combined through scheme switching. We introduce a formal framework that captures security in this setting and provide a rigorous analysis of different constructions. Within this framework, we identify sufficient conditions for the switching algorithm under which the combined schemes achieve IND-CPA-D security, assuming the individual schemes are IND-CPA-D-secure. We then focus on the specific case of scheme switching from CKKS to TFHE. We analyze how existing switching algorithms designed for vanilla CKKS can be modified to preserve IND-CPA-D security. We demonstrate an attack against the IND-CPA-D security of the PEGASUS construction [LHHMQ21] and we implement a proof-of-concept of this attack against the CKKS-to-FHEW switching mechanism in the OpenFHE library. Finally, we present a generic transformation that converts a vanilla CKKS-based switch into an IND-CPA-D-secure one.
@misc{cryptoeprint:2026/285, author = {Santato, Giacomo and Zanotto, Riccardo}, title = {How (not) to Switch {FHE} Schemes: Framework and Attacks in the {IND}-{CPA}-D Model}, howpublished = {Cryptology {ePrint} Archive, Paper 2026/285}, year = {2026}, url = {https://eprint.iacr.org/2026/285}, }
2025
- EUROCRYPT
 Non-interactive Blind Signatures from RSA Assumption and MoreLucjan Hanzlik, Eugenio Paracucchi, and Riccardo ZanottoIn Advances in Cryptology – EUROCRYPT 2025, 2025
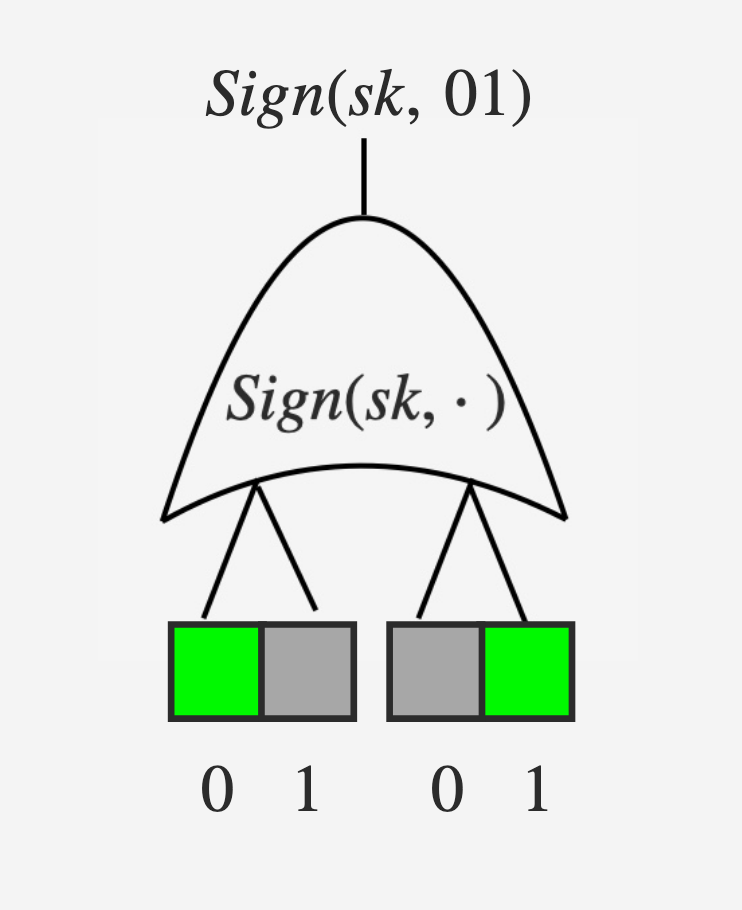
Non-interactive Blind Signatures from RSA Assumption and MoreLucjan Hanzlik, Eugenio Paracucchi, and Riccardo ZanottoIn Advances in Cryptology – EUROCRYPT 2025, 2025Blind signatures have received increased attention from researchers and practitioners. They allow users to obtain a signature under a message without revealing it to the signer. One of the most popular applications of blind signatures is to use them as one-time tokens, where the issuing is not linkable to the redeeming phase, and the signature under a random identifier forms a valid token. This concept is the backbone of the Privacy Pass system, which uses it to identify honest but anonymous users and protect content delivery networks from botnets.
@inproceedings{10.1007/978-3-031-91124-8_13, author = {Hanzlik, Lucjan and Paracucchi, Eugenio and Zanotto, Riccardo}, editor = {Fehr, Serge and Fouque, Pierre-Alain}, title = {Non-interactive Blind Signatures from RSA Assumption and More}, booktitle = {Advances in Cryptology -- EUROCRYPT 2025}, year = {2025}, publisher = {Springer Nature Switzerland}, address = {Cham}, pages = {365--394}, isbn = {978-3-031-91124-8}, doi = {10.1007/978-3-031-91124-8_13}, }
2024
- PKC
 Rate-1 Fully Local Somewhere Extractable Hashing from DDHIn Public-Key Cryptography – PKC 2024, 2024
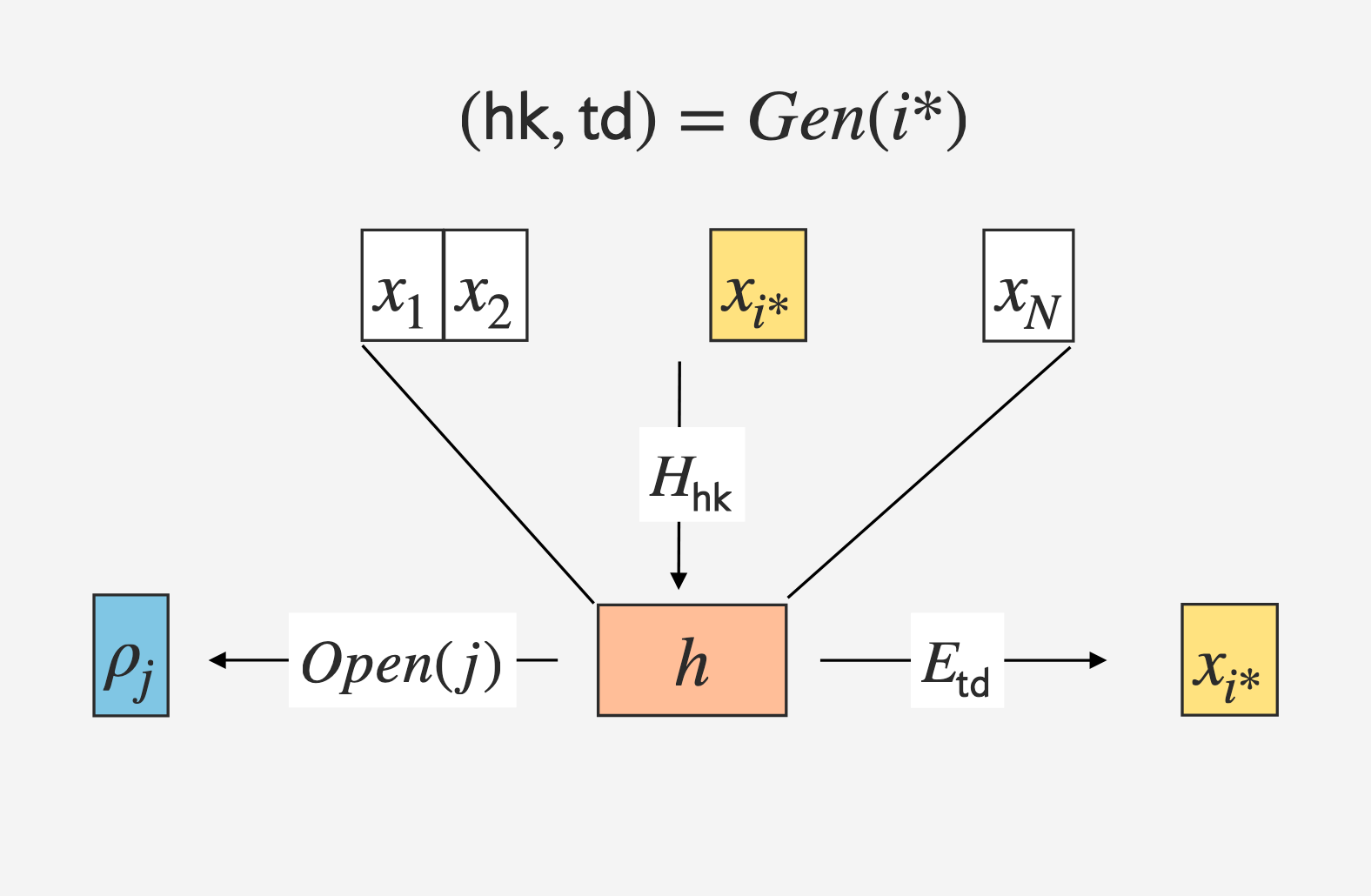
Rate-1 Fully Local Somewhere Extractable Hashing from DDHIn Public-Key Cryptography – PKC 2024, 2024Somewhere statistically binding (SSB) hashing allows us to sample a special hashing key such that the digest statistically binds the input at m secret locations. This hash function is said to be somewhere extractable (SE) if there is an additional trapdoor that allows the extraction of the input bits at the m locations from the digest.
@inproceedings{10.1007/978-3-031-57725-3_12, author = {Branco, Pedro and D{\"o}ttling, Nico and Srinivasan, Akshayaram and Zanotto, Riccardo}, editor = {Tang, Qiang and Teague, Vanessa}, title = {Rate-1 Fully Local Somewhere Extractable Hashing from DDH}, booktitle = {Public-Key Cryptography -- PKC 2024}, year = {2024}, publisher = {Springer Nature Switzerland}, address = {Cham}, pages = {356--386}, isbn = {978-3-031-57725-3}, doi = {10.1007/978-3-031-57725-3_12}, } - CiC
 Simple Two-Message OT in the Explicit Isogeny ModelEmmanuela Orsini and Riccardo ZanottoIACR Communications in Cryptology, 2024
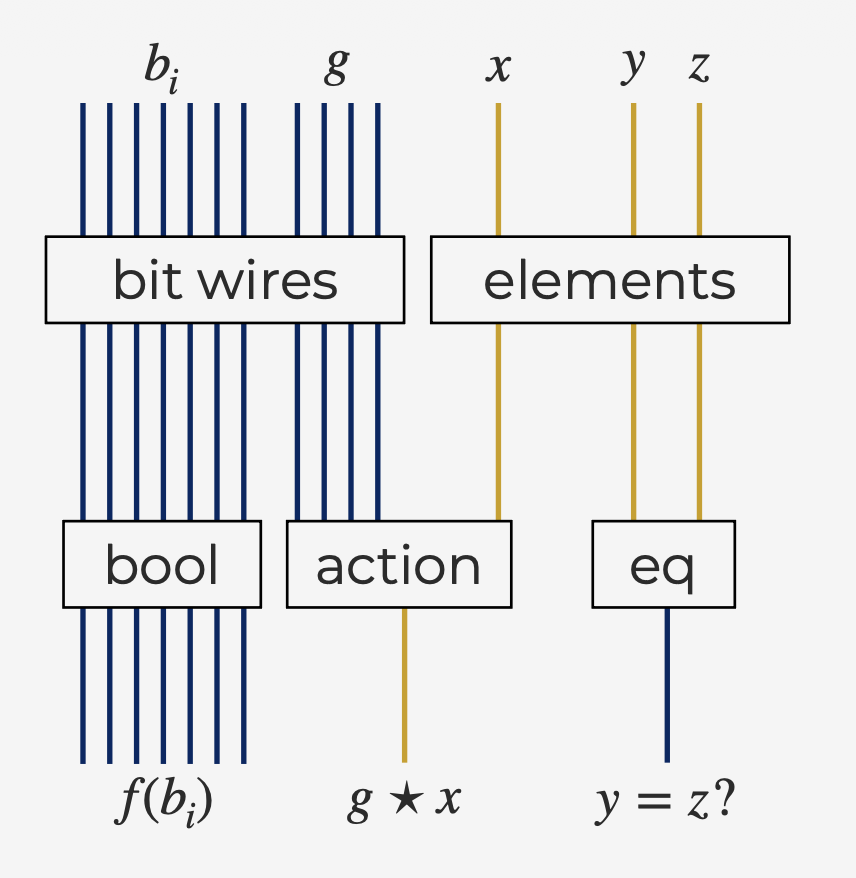
Simple Two-Message OT in the Explicit Isogeny ModelEmmanuela Orsini and Riccardo ZanottoIACR Communications in Cryptology, 2024In this work we study algebraic and generic models for group actions, and extend them to the universal composability (UC) framework of Canetti (FOCS 2001). We revisit the constructions of Duman et al. (PKC 2023) integrating the type-safe model by Zhandry (Crypto 2022), adapted to the group action setting, and formally define an algebraic action model (AAM). This model restricts the power of the adversary in a similar fashion to the algebraic group model (AGM). By imposing algebraic behaviour to the adversary and environment of the UC framework, we construct the UC-AAM. Finally, we instantiate UC-AAM with isogeny-based assumptions, in particular the CSIDH action with twists, obtaining the explicit isogeny model, UC-EI; we observe that, under certain assumptions, this model is "closer" to standard UC than the UC-AGM, even though there still exists an important separation. We demonstrate the utility of our definitions by proving UC-EI security for the passive-secure oblivious transfer protocol described by Lai et al. (Eurocrypt 2021), hence providing the first concretely efficient two-message isogeny-based OT protocol in the random oracle model against malicious adversaries.
@article{10.62056/a39qgy4e-, author = {Orsini, Emmanuela and Zanotto, Riccardo}, title = {Simple Two-Message {OT} in the Explicit Isogeny Model}, volume = {1}, number = {1}, year = {2024}, date = {2024-04-09}, issn = {3006-5496}, doi = {10.62056/a39qgy4e-}, journal = {{IACR} Communications in Cryptology}, publisher = {International Association for Cryptologic Research}, }